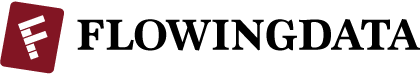
When you use the same password for every online account, there could be trouble down the line if one of those sites was breached. You gotta mix it up these days. As part of their Watchdog initiative, Mozilla released an add-on to help you see how you’re reusing passwords, and to hopefully keep your personal information secure.
Ever been told not to reuse the same password across different websites? With this add-on, you can visualize your passwords and the sites you use them on. By looking at this visualization, you can get a quick idea of which passwords you’ve been using the most, and the kinds of sites you’re using them on. As you continue to change your passwords and update your password manager, the picture will improve!
Personally, I don’t save any of my passwords. The risk of my computer getting stolen and some random person gaining access to my online accounts is too much for me to handle. Of course as a result, I have to put up with the craptastic experience of trying to remember passwords with a variable number of capital letters, symbols, and digits.
[Mozilla]
 Visualize This: The FlowingData Guide to Design, Visualization, and Statistics (2nd Edition)
Visualize This: The FlowingData Guide to Design, Visualization, and Statistics (2nd Edition)

You could always use LastPass for your passwords – stores them securely in the cloud and you only have to remember a single master password (although for added security I also use YubiKey for 2-factor authentication)
I don’t think Cloud storage is any safer than an on-box password manager – I’d be less likely to trust Cloud security.
Use a password manager; aren’t these built into most browsers these days? Provided it’s implemented properly, your website passwords will be safely encrypted behind a master password, so even if your computer is stolen, your website passwords won’t be compromised.
Here is a neat little password trick: use a base password and append / prepend it with some site specific information. Take the base password “test” for example (a bad password but yet get the idea) and now prefix it with the first letter of the domain and add the last letter of the domain to the end. For this site you password would be “FtestA” for example. Voila, unique passwords and still easy to remember. Don’t use the exact same prefix and suffix as I described here off couse, use some pattern only you know.
Right there with you. I use a base password with mixed alpha-cap-numeric-special and postpend a mnemonic site tag (a non-obvious, only-I-would-think-of-it tag). It makes it easy to remember multiple high-strength passwords, if your base is complex enough, you meet the alphabet soup rules, and you’re pretty much guaranteed to break 10 characters – 12 is recommended these days, is what I’m hearing.
I concur with Nick that LastPass is great – but they still strongly recommend you do not reuse passwords – even within their service.
But long random strings of characters are not necessary. The security of a password against cracking (only one issue – but the one addressed by complexity and length) is based on entropy not memory. With some notable exceptions (‘qwerty’, ‘123456’, ‘password’) cracking is not based on guessing.
The biggest security fallacy is the (false) intuition that the harder a password is to remember the harder it is to crack.
Thats not actually true. The password, “I-can’t-believe-it’s-not-butter” is quite literally orders of magnitude harder to crack than “@#23-DgF” and a hell of a lot easier to remember. Human beings have incredible memories – but we remember through meaning. Add meaning and the level of entropy we can overcome increases exponentially.
We all have already at our disposal thousands of very secure password strings with enough entropy to make them virtually uncrackable by man or machine. Television alone is a gold mine: “Have-a -yabba-dabba-do-time”, “Missed-me-by-that-much”, “Shoot-him-now-shoot-him-now”, “These-are-the-voyages-of-the-starship-enterprise”.
If you still feel vulnerable because these seem more ‘guessable’ then just personalise the mix: “Faster-than-a-speeding-tree-frog”, “Faster@than@a@speeding@tree@frog”, “FasterThan2SpeedingTreeFrogs”. Just use a consistent ‘template” for substituting spaces, numbers capitalisation and punctuation and there will be no additional burden on your memory. Or if all that isn’t enough you can go poetic: “Greasy-horse-feathers-disgust-me”. You can make up phrases that suit the site or services you are accessing for additional mnemonic strength: For example a social network login could be “So-many-idiots-so-few-insults”, or a banking login could “If-I-was-rich-I’d-buy-some-good-friends”
You don’t have to fight the way your brain works to create safe high-entropy passwords, or a much larger number of passwords that are easy to remember. (Of course if you only login to something three times a year you could forget the easiest password – for those use a secure wallet or service to encrypt and save it for later reference. But then, if you do only use a site three times a year the reset my password trip to email is likely not that annoying.)
And here is my whole comment in a more user-friendly format http://xkcd.com/936/
I use 1Password. It’s a platform specific password manager, that can be used across platforms via DropBox. I’m not sure this quite counts as using it in the cloud. I never have to remember any passwords.